Category Archives: Group Policy
Group policy search tool (GPS)
بسم الله الرحمن الرحيم
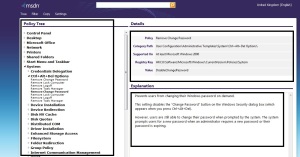
GPS is a online group policy search tool for Microsoft Active Directory Group Policy Settings.
You are unsure whether a policy for your setting exists. you have ever tried to find the registry setting for a specific group policy setting.
With the help of Group Policy Search you can easily find existing Group Policies and find the registry setting for a specific group policy
Group Policy Search will give you what you need. Try it Here
- GPS page overview
- You can change the display and search language
- You can change Tree view (policy view or Registry view)
- You can filter the search to specific products and/or versions
- You can share using the one-click copy feature in the copy menu

- You can add a Search Provider and a Search Accelerator for your Internet Explorer or a Search Connector for your Windows 7
How to Prevent Authenticated Users from joining Workstations to a Domain
بسم الله الرحمن الرحيم
I asked myself what is benefit from this option “by default, Windows Server allows authenticated users to join 10 machine accounts to the domain”. But I didn’t get an answer
Administrator can control it with two ways:
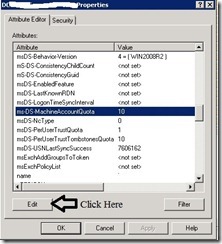
1-By Adsiedit:
- Start – Administrative Tools – ADSI Edit
- Right click Domain Name – Properties
- Attribute Editor Tab – ms-DS-MachineAccountQuota – Click Edit – set to 0 –press ok
Note:
That users in the Administrators or Domain Administrators groups, and those users who have delegated permissions on containers in Active Directory to create and delete computer accounts, are not restricted by this limitation.
2-By Group Policy:
- Click Start – All programs – Administrative Tools – Group Policy Management.
- Create or Edit Group Policy Objects.
- Expand Computer Configuration – Policies – Windows Settings – Security Settings – User Rights Assignment
- From right pane right click on Add workgroup to domain – Properties – Add User or Group or remove unwanted user or group
How to configure AppLocker Group Policy to prevent software from running
بسم الله الرحمن الرحيم
Firstly: What is AppLocker?
AppLocker is a set of Group Policy settings that evolved from Software Restriction Policies, to restrict which applications can run on a corporate network, including the ability to restrict based on the application’s version number or publisher.
- Click Start – All programs – Administrative Tools – Group Policy Management.
- Create or Edit Group Policy Objects.
- Expand Computer Configuration – Policies – Windows Settings – Security Settings – Application Control Policies – AppLocker .
- In right pane click on Configure rule enforcement
Note:
-
Executable rules: .exe, .com
-
Windows Installer rules: .msi, .msp
-
Scripts rules: .ps1, .bat, .cmd, .vbs, .js
- Under Executable rules check configured box and select Enforce rules then click ok

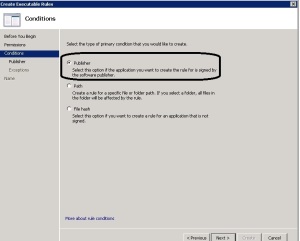
- In left pane under AppLocker right click on Executable Rules then select Create New Rule
- Select Deny and select what user or group will prevent.
Note:
Publisher rules: This condition identifies an application based on its digital signature and extended attributes. The digital signature contains information about the company that created the application (the publisher). The extended attributes, which are obtained from the binary resource, contain the name of the product that the application is part of and the version number of the application.
Path rules: This condition identifies an application by its location in the file system of the computer or on the network.
File hash: This condition identifies an application which is not digitally signed can be restricted by a file hash rule instead of a publisher rule.
- Select Publisher and click Next
- Click browse then select executable file example.exe
- Choose any options from prevent with any publisher, publisher, product name, file name and file version then click Next.
- Read it and click Next
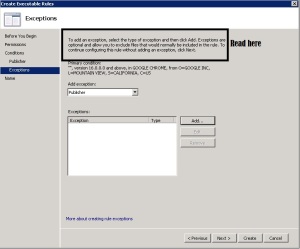
- Click Create

- You will now be prompted to create some default rules that ensure that you don’t accidently stop Windows from working. Click “Yes” to this if you don’t already have these rules created.

Note:
If you want to apply this role on computer administrator then right-click on the BUILTIN\Administrators rule and click Delete
Now we will active the Application Identity service to enable AppLocker on the computers
- In the same Group Policy Object you were just editing Computer Configuration – Policies – Windows Settings – Security Settings – System Services
- Right click Application Identity service then properties
- Check Define this policy setting box and Automatic then OK.

Now when users try run program he will get this
Reference:
http://www.windows7library.com/blog/security/applocker-part-2-understanding-applocker-rules/
How to force proxy settings via group policy
بسم الله الرحمن الرحيم
This article describes how to force proxy settings via group policy.
- Click Start – All programs – Administrative Tools – Group Policy Management.
- Create or Edit Group Policy Objects.
- Expand User configuration – Policies – Windows Settings – Internet Explorer Maintenance – Connection.
- In right Pane Proxy Settings.

For some security reasons maybe administrator need to prevent end users from change their proxy settings
You can do it with group policy follow this steps:
How to (Enable or Disable) Remote Desktop via Group Policy Windows 2008
بسم الله الرحمن الرحيم
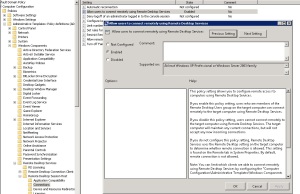
1– We can use Group Policy setting to (enable or disable) Remote Desktop
- Click Start – All programs – Administrative Tools – Group Policy Management.
- Create or Edit Group Policy Objects.
- Expand Computer Configuration – Administrative Templates – Windows Components – Remote Desktop Services – Connections.
- Allow users to connect remotely using Remote Desktop Services (enable or disable)
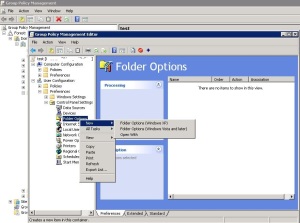
2- We can use Group Policy Preferences to (enable or disable) Remote Desktop
- Click Start – All programs – Administrative Tools – Group Policy Management.
- Create or Edit Group Policy Objects
- Expand Computer Configuration – Preferences – Windows Settings.
- Right click Registry – New – Registry Item.
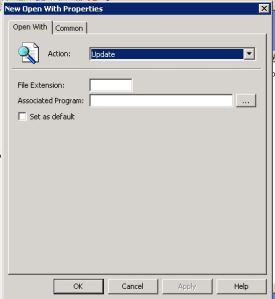
- General Tab.
- Action :Update
- Hive :HKEY_LOCAL_MACHINE
- Key path : SYSTEM\CurrentControlSet\Control\Terminal Server
- Value name : fDenyTSConnections
- Value type : REG_DWORD
- Value date : 00000000 enable OR 00000001 disable
How to Change Local Administrator Password with Group Policy
بسم الله الرحمن الرحيم
We will use Group Policy Preferences to set password on local user accounts.
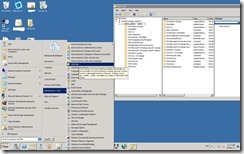
- Click Start – All programs – Administrative Tools – Group Policy Management.
- Create or Edit Group Policy Objects.
- Expand Computer Configuration – Preferences – Control Panel Settings.
- Right click on Local Users and Groups – New – Local User.
Note: Group policy update will take 90 min (Default)
If you want change this time follow this method:
- Expand Computer Configuration – Administrative Templates –System – Group policy
- Enable Group policy refresh interval for computers and set any time you want (Recommended 5 – 10 min)
Or Run this command on clients gpupdate /force
How to Prevent Users from Connecting to a USB Storage Device by Group Policy
بسم الله الرحمن الرحيم
To prevent users from connecting to USB storage devices by group policy
If a USB storage device is already installed on the computer:
- Click Start – All programs – Administrative Tools – Group Policy Management.
- Create or Edit Group Policy Objects
- Expand Computer Configuration – Preferences – Windows Settings.
- Right click Registry – New – Registry Item.
- General Tab.
- Action : Update
- Hive : HKEY_LOCAL_MACHINE
- Key path : SYSTEM\CurrentControlSet\Services\UsbStor
- Value name : Start
- Value type : REG_DWORD
- Value data : 00000004
Notes: You can apply this method on User Configration too.
If a USB storage device is not already installed on the computer:
- Click Start – All programs – Administrative Tools – Group Policy Managment.
- Create or Edit Group Policy Objects
- Expand Computer Configuration – Police – Windows Settings – Security Settings .
- Right click File System– Add file or folder.
- Browse to this file
- %SystemRoot%\Inf\Usbstor.pnf
- assign the user or the group and the local SYSTEM account Deny permissions.
6. Browse to this file too.
- %SystemRoot%\Inf\Usbstor.inf
- assign the user or the group and the local SYSTEM account Deny permissions.